Tech
Linuxia: A Comprehensive Guide to the Linux Operating System

1. Introduction to Linux
Linux is a Unix-like operating system that is open-source and free to use. It was created by Linus Torvalds in 1991 and has since grown into a powerful and versatile operating system.
2. History of Linux
Linux has its roots in the Unix operating system, which was developed in the 1970s at Bell Labs. Linus Torvalds, a Finnish computer science student, created Linux as a hobby project, releasing the first version in 1991. Since then, Linux has been developed collaboratively by thousands of developers worldwide.
3. Features of Linux
Linux is known for its stability, security, and flexibility. It can run on a wide range of hardware, from smartphones to supercomputers. Linux also supports a variety of file systems, including ext4, XFS, and Btrfs, and has a robust security model.
4. Linux Distributions
There are many different distributions, or “distros,” of Linux, each with its own set of features and software packages. Some popular distros include Ubuntu, Fedora, and CentOS. Each distro is tailored to different user needs, such as desktop use, server use, or security.
5. Installing Linux
Installing Linux is relatively straightforward, with most distros offering graphical installers. However, it’s important to back up your data before installing Linux, as the process will erase your hard drive.
6. Linux Command Line Basics
The Linux command line, or shell, is a powerful tool for interacting with the operating system. Users can use commands to perform tasks such as navigating the file system, managing software, and configuring the network.
7. File System Navigation in Linux
Linux uses a hierarchical file system, similar to Unix. Users can navigate the file system using commands such as cd (change directory) and ls (list files).
8. Managing Software in Linux
Linux uses package managers to install, update, and remove software. Different distros use different package managers, such as apt (Debian-based distros) and yum (Red Hat-based distros).
9. User and Group Management in Linux
Linux uses a system of users and groups to control access to resources. Users can belong to one or more groups, which determine their permissions.
10. Network Configuration in Linux
Linux supports a variety of network configurations, including Ethernet, Wi-Fi, and VPNs. Users can configure their network settings using tools such as ifconfig and NetworkManager.
11. Security in Linux
Linux is known for its strong security features, including built-in firewalls and user account controls. Users can also enhance security by keeping their system up to date and using strong passwords.
12. Linux Shell Scripting
Shell scripting allows users to automate tasks in Linux. By writing scripts, users can save time and effort by automating repetitive tasks.
13. Linux Desktop Environments
Linux offers a variety of desktop environments, such as GNOME, KDE, and Xfce. Each desktop environment offers a different look and feel, as well as different features and customization options.
14. Linux for Servers
Linux is widely used as a server operating system, thanks to its stability and security features. Many web servers, such as Apache and Nginx, run on Linux, as do many cloud computing platforms.
15. Conclusion
In conclusion, Linux is a powerful and versatile operating system that offers a wide range of features and customization options. Whether you’re a beginner or an experienced user, Linux has something to offer.
FAQs
- Is Linux free to use? Yes, Linux is open-source and free to use.
- Can I install Linux alongside Windows? Yes, many distros offer dual-boot options that allow you to install Linux alongside Windows.
- Is Linux more secure than Windows? Linux is often considered more secure than Windows due to its strong security features and open-source nature.
- Can I run Windows software on Linux? Yes, you can use compatibility layers such as Wine to run some Windows software on Linux.
- Which is the best Linux distro for beginners? Ubuntu is often recommended for beginners due to its user-friendly interface and extensive documentation.

Tech
How To Keep Up With The Latest Tech

Do you find it hard to keep up with the latest tech trends and developments? You are certainly not alone in this, as tech has been evolving at breakneck speed in recent years, which can make it hard to stay up to date with the best and latest technologies. Whether you are a tech professional looking to keep up with the latest developments or simply curious about new technology, you should know that there are a few ways that you can keep up with the latest trends and developments. This post will look at the best methods that will help you stay current.
Tech Blogs
One of the quickest and easiest ways to keep up with the latest tech news is to read blogs. Many excellent tech blogs post tech news, interviews, tips, tutorials, and other useful content. Checking these blogs on a regular basis will help you stay abreast of all the latest developments.
Tech Podcasts
Similarly, tech podcasts are a fantastic way to learn about the latest technology. Many popular tech podcasts out there cover all you need to know about the world of tech and often include interviews with key industry figures. Podcasts are great because you can listen to them on the go and while completing other tasks, such as cleaning, driving, or exercising.
Learning Centers
Online learning centers are a great way for those looking to learn about tech and develop their skills. Places like the Kong Learning Centre can provide foundational guides that cover key industry concepts and technologies, which is ideal for developers and other tech professionals looking to sharpen their abilities. Learning how to harness tech can be challenging, so learning centers are ideal for those looking to not just learn about tech but also how to use it yourself.
Social Media
Of course, social media can be an excellent platform for learning about the latest news and developments in the tech world. The key is to follow leading industry organizations and individuals so that your feed will be filled with engaging content that will keep you up to date.
Events
Another way to keep up with the latest tech news is to attend industry events. There are always tech events that will showcase different technologies and give you the chance to learn from industry innovators. Of course, many events take place online these days, allowing people to attend no matter where they are located in the world. These events can also be a good opportunity to grow your network.
Online Communities
Engaging in online communities allows you to speak with other tech enthusiasts from all around the world. This can be a great way to discuss new technologies, ask questions, and feel like part of a large global community.
These are a few of the best ways to keep up with the latest tech trends and developments. Whether you work in tech or you simply have an interest in the latest technologies, these methods will help you stay ahead of the curve and get to grips with the best and latest technologies.
Tech
Best Practices for Electrical Safety in Commercial Buildings
Key Takeaways:
- Understand the importance of electrical safety in commercial environments.
- Learn the essential safety measures to implement in commercial buildings.
- Discover the significance of regular electrical inspections and maintenance.
- Explore the role of employee training in maintaining a safe electrical system.
The Importance of Electrical Safety in Commercial Buildings
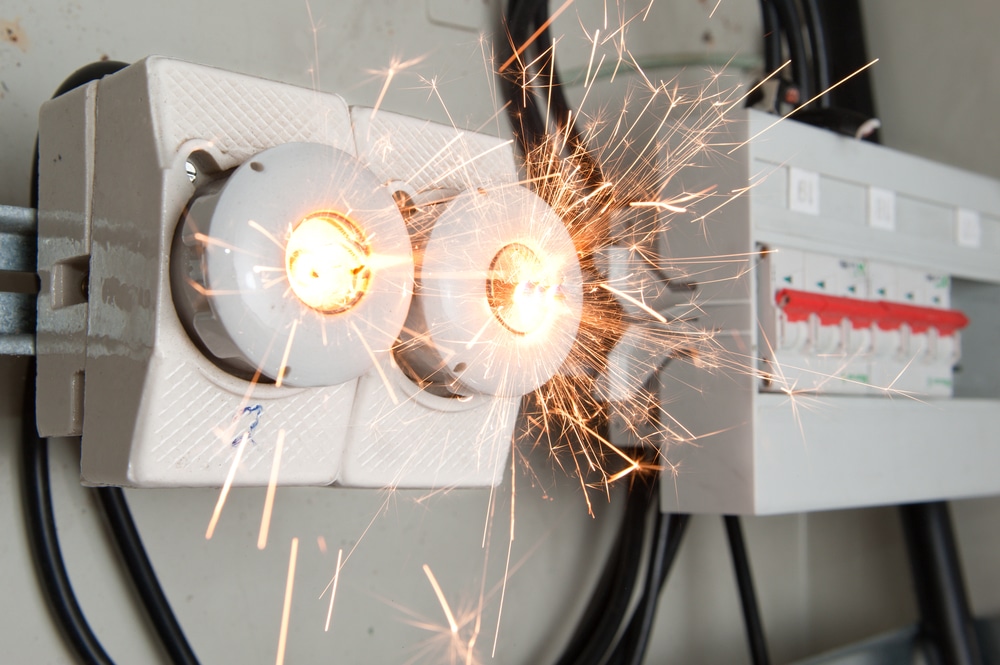
Electrical safety is critical to maintaining a secure and functional commercial environment. Neglecting safety measures can result in severe consequences, including electrical fires, equipment damage, and even human injury. According to the National Fire Protection Association (NFPA), an estimated 15% of fires in commercial properties are caused by electrical failures or malfunctions. Such incidents risk human lives and result in significant financial losses and disruptions to business operations. Therefore, businesses must prioritize electrical safety protocols to safeguard their premises and personnel.
To achieve this goal, many companies seek the expertise of professionals, such as a land development engineer, who can provide comprehensive assessments and recommendations. These experts are adept at identifying potential risks and offering solutions that enhance electrical safety in commercial settings.
Regular Electrical Inspections and Maintenance
Regular inspections and maintenance are key to sustaining electrical safety in commercial buildings. It’s advisable to schedule periodic inspections by qualified professionals who can detect and correct any flaws in the electrical system. These experts are trained to identify issues that may not be immediately apparent, such as wear and tear on wiring, corrosion, or other forms of degradation. Additionally, maintaining a record of all inspections and repairs can help track the condition of electrical components and plan future maintenance effectively. By being proactive, little problems can be stopped before they become bigger ones, protecting the electrical system’s dependability and safety.
Scheduling Periodic Inspections
Depending on the complexity and age of the electrical system, inspections should be done at least once a year, if not more often. These inspections should include testing safety equipment like smoke detectors and alarms, assessing circuit load capacities and checking wiring integrity. Frequent inspections reduce the chance of electrical fires and equipment failures by assisting in the early detection of possible problems.
Maintaining Inspection Records
Keeping detailed records of inspections and repairs can be invaluable. These records help assess the electrical system’s health over time and provide crucial information for planning timely maintenance or upgrades. Additionally, documentation can be useful for complying with safety regulations and standards, ensuring that the business meets all requirements for electrical safety.
Addressing Common Electrical Issues
Common electrical issues in commercial buildings include overloaded circuits, exposed wiring, and outdated equipment. Addressing these issues promptly is vital to prevent disruptions and hazards. Overloaded circuits can lead to frequent tripping of breakers, and exposed wiring poses a danger of electric shock or fire. For instance, replacing old wiring and upgrading to energy-efficient lighting and appliances can significantly reduce the risk of electrical malfunctions and improve overall safety. By proactively addressing these common issues, businesses can maintain a safer and more efficient electrical system.
Overloaded Circuits
An overloaded circuit can cause breakers to trip frequently and lead to overheating, which poses a significant fire hazard. Businesses should ensure that circuits are appropriately rated for their load and avoid plugging too many devices into one outlet. Regular assessments of circuit loads and adjustments as needed can prevent overloads and enhance safety.
Exposed Wiring
Exposed wiring is dangerous as it can easily contact people or flammable materials. Regular inspections should include checks for exposed or damaged wires and repairing them promptly. Electrical accident risk can be considerably decreased by ensuring all wiring is adequately insulated and shielded.
Leveraging Technology for Electrical Safety
Technology is crucial in enhancing electrical safety. Modern advancements, such as smart electrical panels and monitoring systems, allow for real-time tracking of electrical usage and early detection of anomalies. Leveraging these technologies can help businesses avoid potential issues and maintain a safer electrical system. Embracing technological solutions can lead to more efficient management and a greater understanding of electrical systems.
Smart Electrical Panels
Bright panels offer real-time monitoring and control over electrical systems, allowing facility managers to detect irregularities and optimize power distribution efficiently. These panels can provide alerts and notifications when potential issues arise, enabling prompt action to prevent problems from escalating.
Monitoring Systems
Modern monitoring systems can notify staff members of possible issues before they become more serious, allowing for prompt action and lowering the possibility of mishaps or equipment failure. Monitoring systems can measure temperature, current flow, voltage levels, and other factors to provide a comprehensive picture of the electrical system’s state.
Creating an Electrical Safety Culture
Creating a culture of electrical safety within the workplace involves continuous education and vigilance. Encouraging employees to report electrical issues immediately and conducting regular safety drills can reinforce the importance of electrical safety. A proactive approach ensures that safety remains a top priority and minimizes the risk of accidents. Fostering a safety-first mindset among employees can lead to a more compliant and aware workforce.
Encouraging Reporting
Encouraging workers to report electrical problems in a comfortable environment can expedite the treatment of minor issues and keep bigger hazards at bay. Employees can efficiently voice issues by implementing a reporting system that is easy to understand and accessible.
Regular Safety Drills
Regular safety drills ensure that all employees are prepared to respond appropriately in an electrical emergency, enhancing workplace safety. Drills should be designed to simulate real-life scenarios and provide practical experience in handling emergencies.
Conclusion
Upholding electrical safety in business buildings is a continuous duty that calls for attention to detail and preemptive action. Businesses may dramatically lower the risk of electrical dangers by making frequent inspections a priority, putting in place crucial safety procedures, and providing employee training.
Tech
Powering Your Business into the Future: How to Seamlessly Transition to Commercial Solar Energy

As the globe becomes increasingly conscious of environmental sustainability and the economic pressures of operating a business, companies are looking for ways to cut costs and reduce their carbon footprint. One viable solution that is gaining traction is the transition to solar power. In this pursuit, understanding the multitude of benefits and considerations is critical for business leaders who are interested in making an informed decision. The focus of this article is to guide your business through the seamless adoption of solar panels for business, the economic gains, and the crucial role a consultancy firm like Johnson Energy Consulting can play in this process.
Understanding the Economic Advantages
Investing in solar energy is not just a nod to environmental stewardship; it’s a strategic financial decision as well. Solar panels can provide a substantial reduction in electricity bills, delivering real savings that can be channelled back into growing your business. Furthermore, there are often government incentives and rebates available which serve to lower the initial setup cost of solar installations.
Yet, understanding the complex landscape of suppliers, technology options, and financial models can prove daunting. That’s where obtaining comprehensive commercial solar quotes plays an integral role. Accurate quotes not only deliver clarity on upfront costs but also provide forecasts on long-term savings and return on investment timelines.
Environmental Commitment as a Business Ethos
Today’s consumers and business partners are increasingly favouring companies with a strong commitment to sustainability. By transitioning to commercial solar energy, businesses send a powerful message that they prioritise global citizenship. Reduced greenhouse gas emissions and lessened dependence on fossil fuels are significant outcomes of this switch, aligning business practices with ecological responsibility.
Assessing Solar Suitability for Your Business
To efficiently transition to solar power, first, your business facilities must be evaluated for solar viability. Key factors to consider include the geographical location, roof integrity, and the orientation, which directly influence the efficiency of the solar panels. Such assessments can sometimes require a high degree of technical expertise.
Navigating Technical Complexities
When considering solar energy, the technical intricacies can seem overwhelming. Different solar panel brands and types offer varying degrees of efficiency, longevity, and warranty conditions. Moreover, the integration of solar power with existing electrical systems can pose additional challenges. This technical minefield underlines the importance of expert consultation to avoid common pitfalls and ensure a system that is tailor-made for your business needs.
Why Choose Johnson Energy Consulting?
To navigate these complexities, partnering with a reputable consultancy such as Johnson Energy Consulting can significantly streamline the process. A consultancy can provide a wealth of industry knowledge, access to trusted suppliers, and manage the entire project – from the initial quotes and assessments through to implementation.
The Role of Consultants in Solar Transition
Consultancy firms specialise in understanding your business requirements, energy usage patterns, and financial objectives to deliver a bespoke solar solution. They work to secure competitive commercial solar quotes, facilitate necessary approvals, and can monitor installation quality and effectiveness post-implementation. This holistic approach ensures not only a transition to solar power but also that your investment yields the expected financial and environmental benefits.
Maximising Your Solar Investment
While the transition to solar can be filled with opportunities, maximisation of your solar investment is key. This requires a strategic approach to sizing your solar system, negotiating purchase or lease agreements, and understanding the intricacies of solar output in relation to your business operations.
A consultancy can also help set up monitoring systems to track solar energy production, usage, and performance over time. These systems ensure your solar panels are performing optimally and help identify any areas that may require maintenance or upgrades.
Long-Term Business Growth and Sustainability
Adopting solar power is not just a move towards sustainability but signifies a commitment to long-term business growth. As energy prices continue to rise, the savings provided by solar energy can become a significant competitive advantage. Moreover, by showcasing a dedication to green initiatives, businesses can enhance their brand reputation and customer loyalty.
In an era where every business decision counts, the integration of solar technology presents an avenue for cost savings, operational efficiency, and environmental responsibility. Obtaining the right solar panels for business is more than an investment in energy; it’s an investment in the future vitality and public image of your company.
Preparing for the Future
As we look forward, renewable energy sources like solar power are slated to become even more integral to business operations. Understanding the full spectrum of benefits and considerations of transitioning to commercial solar power is imperative for future-proofing your business.
Conclusion
The journey to roll out commercial solar energy can be complex, but it doesn’t have to be cumbersome. With the right partner and a comprehensive plan in place, your business can effortlessly make the switch. Embracing solar power with the guidance of seasoned experts like Johnson Energy Consulting will energise your business today and sustain it for decades to come.
Seize the opportunity for growth, resilience, and a greener future by integrating solar energy into your business model. Power your business into the future; begin your journey to clean, sustainable, and cost-effective energy today.
Tech
Top 3 Cross Browser Testing Tools You Should Know

Cross Browser Testingis important when it comes to designing applications for browsers so that the page looks good on all the different devices. Given the number of browsers and versions available, it is simply impractical to go through the process of manually testing a web application across the various combinations. Cross browser testing tools are used at this point. They enable the testing process to be tested across different browsers, which is a very convenient feature that saves a lot of time. Here are the top 3 cross browser testing tools you should consider.
1. Testsigma
Testsigma is a leading intelligent test automation platform with integrated cross-browser testing capabilities. It allows users to write test scripts in simple English, which can run on multiple browsers and devices without modifications. Key features include browser-agnostic scripts that reduce maintenance, a real device cloud with 3000+ options, self-healing scripts that adapt to application changes, and comprehensive reporting for easy failure tracing.
Testsigma’s integration features enable continuous testing across browsers, supporting frequent testing and high-quality web application releases. This platform empowers teams to shift testing left in the development process, enhancing overall software quality and efficiency. Testsigma’s user-friendly approach and advanced capabilities make it a top choice for organizations seeking to streamline their cross-browser testing processes and improve their web application development workflow.
2. Testim
Testim is an automated testing tool for web and mobile applications, offering high-speed cross-browser testing. Its integrated recorder simplifies test script creation without coding. Key features include parallel execution across multiple browsers and devices for rapid results, advanced root cause analysis for quick debugging, robust connectors for integration with CI/CD tools DevOps, and an automated bug tracker that logs issues with screenshots and step-by-step guides.
Testim accelerates test cycles through parallel testing and intelligent test generation based on past executions. This approach enables organizations to shift testing left in the development process, facilitating faster delivery of reliable web applications. Testim’s combination of user-friendly features and advanced capabilities makes it an efficient solution for teams looking to streamline their testing processes and improve overall software quality.
3. Ranorex Studio
Ranorex Studio is a leading GUI and cross-browser testing tool suitable for enterprise-level application testing on desktop and mobile browsers. It offers a click-and-record feature for creating test automation scripts without coding. Key features include broad browser coverage for testing on current and past versions of desktop and mobile browsers, dynamic recognition of test objects even after application changes, comprehensive reporting with detailed failure information, and workflow integration with CI/CD tools.
Ranorex Studio’s integration capabilities enable sequential and continuous cross-browser testing, allowing teams to run tests across multiple browsers early in the development cycle for quick results. This comprehensive approach to testing, combined with its user-friendly interface and robust features, makes Ranorex Studio an effective solution for organizations seeking to enhance their cross-browser testing processes and improve overall software quality.
Conclusion
Ensuring that web testing is done across browsers frequently is an essential feature in creating optimal user experiences. The automated cross browser testing such as Testsigma, Testim and Ranorex studio enable the left shifting of testing, testing across browsers at an early stage and releasing high quality web applications in the market. All of these tools support cross browser testing, but with Testsigma coming out slightly ahead due to its no code, auto healing and easy to use platform.
Tech
What Key Factors Contribute to the Widespread Use of Evo Mosquito Repeller?

The EVO Mosquito Repeller has won a great reputation as a cutting-edge solution for mosquito control, blending innovation with practicality. Designed to repel mosquitoes with the use of superior ultrasonic technology, it emits high-frequency sound waves that disrupt mosquito sensory organs, correctly deterring them without causing any damage to human beings or pets. This chemical-loose technique resonates nicely with environmentally aware purchasers in search of secure alternatives to traditional repellents.
Its reputation stems from its twin capabilities: not only does it repel mosquitoes, but it additionally serves as a versatile outdoor lantern with an effective 3000 lm output. This makes it best for illuminating campsites, backyard gatherings, and middle-of-the-night adventures while concurrently keeping mosquitoes at bay. The tool’s compact and lightweight design enhances its portability, ensuring convenience throughout the journey and out-of-door activities.
User delight is evident in high-quality opinions highlighting its effectiveness and simplicity of use. The EVO Mosquito Repeller has grown to be a relied-on accomplice for outdoor fans, families, and house owners alike, offering dependable mosquito protection without the inconvenience of chemical sprays or lotions. As the focus on its benefits spreads, the evo mosquito repellent keeps growing in popularity as a sensible and sustainable preference for mosquito management, putting new popularity in outside consolation and safety.
Factors Contributing to Widespread Use of Evo Mosquito Repeller
The significant use of EVO mosquito repeller can be attributed to several key elements that collectively enhance their attraction to a huge spectrum of customers. These elements include their effectiveness, convenience, protection, versatility, and high-quality persona. In this article, we can discover those components and recognize why EVO mosquito repeller have turned out to be a popular preference for mosquito control.
- 3-in-1 with Double-Sided Design
The EVO Mosquito Repeller features a 3-in-1 capability with a double-sided design, providing superior versatility. One facet repels mosquitoes through the use of ultrasonic generation, just as the other aspect is capable of being an effective LED flashlight. Moreover, it includes a rechargeable battery that powers each feature, making it a handy and multi-purpose device for outdoor activities. This revolutionary design guarantees you live protected from mosquitoes whilst also imparting reliable lights, all in a compact and transportable device.
- Dual-Protection Mode with 50s Fast Heating
The EVO Mosquito Repeller boasts a dual-safety mode that provides enhanced mosquito defense. With its modern 50-2nd rapid heating feature, the device quickly reaches the most appropriate temperature, freeing mosquito-repelling agents correctly. This rapid activation guarantees on-the-spot safety, making it ideal for outdoor activities. The twin modes allow customers to switch between standard and excessive-intensity repellent settings, catering to varying mosquito densities. To read more about EVO Mosquito Repeller see the details below.
- 3000lm Ultralight Outdoor Lantern
The EVO Mosquito Repeller consists of a 3000-lm ultralight out-of-door lantern, presenting effective illumination for any outside location. Despite its excessive brightness, the lantern is relatively lightweight, making it easy to carry on camping journeys, hikes, or evening backyard gatherings. Its twin capability as a mosquito repeller and a lantern guarantees you’ve got the essential mild at the same time to stay protected from mosquitoes. The 3000 lm output gives you clean visibility, improving safety and convenience throughout middle-of-the-night activities.
- Long Endurance with Power-Bank
The EVO Mosquito Repeller provides long-term persistence with its integrated power bank characteristics, ensuring prolonged protection and convenience. The integrated electricity bank allows you to recharge your devices on the go, making it a vital device for outdoor adventures. With its long-lasting battery life, the repeller presents continuous mosquito protection, reducing the need for common recharges. This twin capability of mosquito repelling and tool charging makes the EVO Mosquito Repeller a flexible and sensible addition to your tools.
- Reduced Carbon Footprint
The EVO Mosquito Repeller contributes to a reduced carbon footprint by imparting a sustainable opportunity to chemical repellents. Its long-lasting battery minimizes the need for disposable batteries, while its long-lasting creation reduces waste over the years. Due to the tool’s rechargeable nature, fewer resources are needed for production and disposal. By deciding on the EVO Mosquito Repeller, users support efficiency that ensures effective mosquito safety with minimal environmental impact. This commitment to sustainability makes it a perfect preference for environmentally conscious individuals.
- Positive User Feedback
The EVO Mosquito Repeller constantly gets tremendous comments, with many praising its effectiveness and simplicity of use. Customers recognize its dual functionality as both a mosquito repeller and an outdoor lantern, noting its reliability during tenting journeys and backyard gatherings. The iconic battery and power bank characteristics are also surprisingly valued. Standard, customers record a big reduction in mosquito bites, making the EVO Mosquito Repeller a depended-on and advocated choice for out-of-doors safety.
- Adaptability to Different Environments
The EVO Mosquito Repeller excels at adapting to various environments, making sure powerful mosquito control anywhere it is used. Whether or not in urban settings, suburban neighborhoods, or remote wasteland regions, its ultrasonic era provides dependable safety against mosquitoes. The tool is similarly powerful in diverse climates and geographical conditions, making it a versatile desire for outside fanatics, tourists, and people alike looking for steady and adaptable mosquito-repellent solutions.
- Indoor and Outdoor Use
The EVO Mosquito Repeller is designed for indoor and outdoor use, providing versatile mosquito protection in any surroundings. Interiorly, it effectively keeps mosquitoes at bay in bedrooms, living rooms, and different indoor spaces. Exteriorly, it presents dependable defense throughout camping, trekking, picnics, and outdoor gatherings. Its twin capability ensures non-stop safety wherever you cross, making it a handy desire for preserving a mosquito-unfastened environment in each interior of your private home and outside settings.
- Advanced Technology
The EVO Mosquito Repeller carries advanced ultrasonic technology to repel mosquitoes successfully. Emitting excessive-frequency sound waves that are innocent to human beings but traumatic to mosquitoes disrupts their sensory mechanisms and forestalls them from coming near. This technology is primarily based on medical studies and ensures a chemical-free, non-toxic approach to mosquito manipulation. Users benefit from dependable safety against mosquitoes without the need for harmful chemicals, improving safety and luxury in both indoor and outdoor environments.
Summary
The massive use of EVO mosquito repeller can be attributed to a mixture of things that make them an attractive choice for mosquito control. Their effectiveness, convenience, safety, versatility, and fine personal comments have all contributed to their popularity. Moreover, their environmental friendliness, cost-effectiveness, and wide market reach make certain that they remain a favored option for individuals in search of dependable and sustainable mosquito protection. As awareness of their benefits keeps developing, EVO mosquito repeller are likely to see even more adoption in the future.
Tech
Översägt: The Evolution And Importance Of Communication

In an age where communication is paramount, Översägt has emerged as a revolutionary platform reshaping how we connect, share, and interact. This article delves into the evolution of Översägt, exploring its transformative impact on global communication.
The Genesis of Översägt
Översägt, a Swedish term meaning “overstated,” began as a simple idea aimed at enhancing the clarity and efficiency of communication. Founded in 2018 by a team of linguists, software engineers, and communication experts, the platform was designed to address the growing complexity and volume of digital interactions. The founders recognized that in a world inundated with information, there was a need for a tool that could streamline conversations, making them more concise and meaningful.
Evolution of the Platform
Initial Phase: Text Simplification The early version of Översägt focused on text simplification. Using advanced natural language processing (NLP) algorithms, the platform could analyze lengthy texts and condense them into concise summaries without losing essential information. This feature quickly gained popularity among professionals, students, and anyone needing to process large volumes of information efficiently.
Expansion to Multilingual Capabilities Recognizing the global nature of communication, Översägt expanded its capabilities to include real-time translation and multilingual support. This feature allowed users to communicate seamlessly across language barriers, fostering international collaboration and understanding. By integrating machine learning and AI, Översägt ensured that translations were accurate and contextually appropriate.
Incorporation of Voice and Video With the rise of video conferencing and remote work, Översägt adapted by incorporating voice and video communication tools. The platform’s ability to transcribe and summarize meetings in real-time became a game-changer for businesses and educational institutions. This innovation not only saved time but also enhanced productivity by allowing participants to focus on the discussion rather than note-taking.
The Importance of Communication in the Digital Age
Enhanced Collaboration Översägt has significantly enhanced collaboration by breaking down language barriers and simplifying complex information. Teams across different time zones and linguistic backgrounds can now work together more effectively, leading to increased innovation and productivity.
Informed Decision-Making The ability to quickly access and understand information is crucial in today’s fast-paced world. Översägt’s summarization and translation tools enable users to make informed decisions based on comprehensive yet concise data. This is particularly valuable in fields such as medicine, law, and finance, where timely and accurate information is critical.
Educational Advancement Educational institutions have also benefited from Översägt’s capabilities. Students and educators can access resources in multiple languages, engage in international research collaborations, and utilize the platform’s summarization tools to better understand complex subjects. This has democratized access to knowledge and fostered a more inclusive learning environment.
Enhanced User Experience By prioritizing user experience, Översägt has set a new standard for communication tools. Its intuitive interface, coupled with powerful AI-driven features, ensures that users can communicate more effectively and efficiently. This focus on user-centric design has been instrumental in the platform’s widespread adoption.
The Future of Översägt
As Översägt continues to evolve, its potential applications are vast. The integration of augmented reality (AR) and virtual reality (VR) could further transform how we communicate, providing immersive and interactive experiences. Additionally, ongoing advancements in AI and machine learning will enhance the platform’s ability to understand and predict user needs, making communication even more seamless and personalized.
In conclusion, Översägt has revolutionized the way we communicate in the digital age. By simplifying complex information, breaking down language barriers, and enhancing collaboration, the platform has proven to be an indispensable tool for individuals and organizations worldwide. As it continues to innovate and expand, Översägt is poised to play an even more significant role in shaping the future of global communication.
Översägt: Frequently Asked Questions (FAQs)
Q1: What is Översägt? A1: Översägt is a comprehensive communication platform that enhances clarity and efficiency in digital interactions. It offers text simplification, real-time translation, voice and video communication, and summarization tools.
Q2: Who founded Översägt? A2: Översägt was founded in 2018 by a team of linguists, software engineers, and communication experts.
Q3: What does the name “Översägt” mean? A3: “Översägt” is a Swedish term meaning “overstated.”
Features
Q4: How does Översägt’s text simplification work? A4: Översägt uses advanced natural language processing (NLP) algorithms to analyze lengthy texts and condense them into concise summaries without losing essential information.
Q5: Can Översägt translate texts in real-time? A5: Yes, Översägt offers real-time translation and multilingual support, allowing seamless communication across language barriers.
Q6: Does Översägt support voice and video communication? A6: Yes, Översägt includes tools for voice and video communication, with real-time transcription and summarization capabilities.
Usage
Q7: Who can benefit from using Översägt? A7: Översägt is beneficial for professionals, students, educators, businesses, and anyone needing to process and communicate large volumes of information efficiently.
Q8: How does Översägt enhance collaboration? A8: By simplifying complex information and providing real-time translation, Översägt enables teams across different time zones and linguistic backgrounds to work together more effectively.
Q9: How can educational institutions use Översägt? A9: Educational institutions can use Översägt to access resources in multiple languages, engage in international research collaborations, and utilize summarization tools for better understanding of complex subjects.
Technical Questions
Q10: Is Översägt secure? A10: Yes, Översägt employs robust security measures to ensure that all communications and data are protected.
Tech
How Technology Is Revolutionizing Inventory Management

Key Takeaways
- The implementation of advanced technology can significantly streamline inventory management processes.
- Using predictive analytics helps in better forecasting and demand planning.
- Technology aids in reducing human errors and increasing efficiency.
The Current State of Inventory Management
Inventory management is a critical function for any business dealing with physical goods. Traditionally, this process was manual and required extensive labor, often leading to errors and inefficiencies. The advent of technology has drastically changed this landscape, providing businesses with tools that can simplify and optimize these tasks. For instance, a robust medical device labeling system solution can significantly enhance accuracy and operational efficiency. Recent research indicates that businesses that use contemporary inventory management systems see significant improvements in performance indicators like order accuracy and inventory turnover.
Benefits of Using Technology in Inventory Management
Integrating technology into inventory management offers numerous benefits. One of the most significant advantages is the enhancement of accuracy. Traditionally, manual inventory tracking methods are prone to human errors, whether through data entry mistakes or miscalculations. With the adoption of advanced software, businesses can automate many of these processes, drastically reducing errors and increasing data reliability. Moreover, technology frees up valuable employee time by automating routine tasks such as stock level monitoring and reorder scheduling. Now, employee focus may be put toward more strategic duties that advance business growth. Inventory management is another area where predictive analytics can be quite important. These tools can predict future trends by analyzing historical data and help businesses better prepare for demand fluctuations. For instance, businesses often face challenges in keeping the right stock levels during peak seasons or marketing campaigns. Predictive analytics can forecast these spikes, ensuring companies maintain optimal inventory levels and reducing the risk of stockouts or overstocking.
How Predictive Analytics Help
Businesses can forecast future trends using predictive analytics, which uses historical data to estimate demand and modify inventory levels accordingly. For example, retailers often experience increased demand during holidays, and predictive analytics can guide them in stocking up on popular items. Predictive models can also help identify slow-moving stock, enabling businesses to implement strategies such as discounts to free up storage space. According to Forbes, companies that adopt predictive analytics for inventory management see notable reductions in stockouts and excess inventory, ultimately leading to improved customer satisfaction and reduced carrying costs.
Automation and Its Role in Efficiency
Automation is another game-changer in the realm of inventory management. Tasks such as ordering, reordering, and tracking inventory can be automated, resulting in consistent and accurate operations. Automated systems can also generate real-time reports that provide insights into inventory levels, sales patterns, and supplier performance. This increases operational efficiency by empowering firms to make fast, data-driven decisions that are well-informed. Furthermore, automation can help set up triggers for reorders, ensuring that stock levels are maintained without manual intervention.
Challenges and Considerations
There are many advantages to using modern technology in inventory management, but there are drawbacks as well. It can be expensive to set up new systems initially, and companies may also need to spend money on employee training. Additionally, data security is a critical consideration. As the systems gather and store vast amounts of data, protecting sensitive business information is paramount. Businesses must also consider the potential for system downtime and the impact it could have on operations. Thus, a comprehensive risk management plan should accompany the implementation of any new technology.
Future Trends in Inventory Management Technology
The future of inventory management technology looks promising, with trends pointing towards even greater automation and the use of artificial intelligence (AI). These advancements are likely to provide even more accurate forecasts and streamlined operations. For instance, AI-powered systems could offer predictive insights that go beyond traditional analytics, identifying emerging trends and anomalies that human analysts might miss. Additionally, the use of IoT (Internet of Things) devices for real-time inventory tracking is expected to become more prevalent, offering businesses unprecedented visibility into their supply chains.
Conclusion
In conclusion, the implementation of advanced technology in inventory management has the potential to revolutionize business operations. By embracing these tools, companies can achieve higher accuracy, better demand forecasting, and enhanced efficiency. Investing in technology optimizes current processes and prepares businesses for future challenges and opportunities, ultimately leading to greater success and sustainability in a competitive market environment.
Tech
Staying Connected Abroad: The Rise of eSIMs and Travel SIM Cards for Seamless Communication in Europe and the UK

For international travellers, staying connected while exploring Europe and the UK has historically come with its set of complications – from the exuberant costs of roaming charges to the inconvenience of swapping physical SIM cards. However, the evolution of digital SIM technologies, such as eSIMs and travel-specific SIM cards, has revolutionised the way globetrotters communicate abroad. In this article, we delve into this groundbreaking shift, highlighting the benefits and sophistication of these digital solutions.
The Advent of eSIM Technology
The term ‘eSIM’ stands for ‘Embedded Subscriber Identity Module’ – a game-changing innovation that’s been gaining popularity among tech-savvy travellers. Unlike traditional SIM cards, eSIMs are built into the device itself, allowing users to switch carriers or plans without the need for a physical card. All that’s needed is to scan a QR code or install a profile from the provider onto your device.
One of the chief advantages of using an eSIM UK-based or otherwise is the seamless transition it offers. For UK residents jetting off to Europe or Europeans exploring the scenic British Isles, an eSIM eliminates the struggle of finding compatible stores, overcoming language barriers, and dealing with multiple SIM cards.
The Growth of eSIMs in Europe and The UK
In Europe and the UK, the adoption of eSIM technology has seen a steady climb. Telecommunication giants in these regions are progressively supporting eSIMs, recognising their value to both consumers and carriers. Consumers enjoy the flexibility of on-the-go plan changes, while carriers benefit from reduced costs associated with producing and distributing physical SIM cards.
The emergence of specialised eSIM providers caters specifically to travellers. These digital services offer short-term, data-centric plans ideal for tourists who don’t require long-term contracts. The convenience of setting up your mobile plan before you even depart is not only reassuring but also efficient, allowing more time to enjoy the travel experience.
The Role of Travel SIM Cards
While eSIMs represent the latest in SIM technology, physical Europe SIM card options still retain their place in the market, especially for those using devices not yet eSIM compatible. These travel SIM cards are tailored for short-term use, offering a variety of data, calling, and texting packages to suit different travel needs.
Furthermore, the advantage of a travel SIM card includes broader compatibility with various phone models and the tangible element of having a backup option should digital setups face technical issues.
Understanding Travel SIM Cards and eSIMs for the Modern Traveller
The primary lure of both travel SIM cards and eSIMs lies in their capacity to provide immediate connectivity. They mitigate the shock of post-holiday phone bills with transparent, upfront costs and the ease of preloading data. For those documenting their European adventures or needing to stay in touch with loved ones, this is paramount to a hassle-free travel experience.
Moreover, as the travel industry becomes increasingly globalised, the importance of uninterrupted communication cannot be underestimated. Keeping abreillesestynd connected to essential services such as navigation, accommodation bookings, and travel updates ensures a safer, more enjoyable journey.
Choosing the Right SIM Option for Your Next Trip
Deciding between an eSIM and a Travel SIM card ultimately boils down to personal preference and tech compatibility. For those with newer smartphones, embracing eSIM technology is a no-brainer. It aligns with the pursuit of minimalist travel – eliminating one more item from your physical inventory.
Those with devices not yet eSIM capable or who prefer physical SIMs can opt for a travel SIM card, providing the same level of connectivity with a touch more tradition. Whichever you choose, both options offer a multitude of benefits designed to keep you connected while you roam abroad.
Embracing Seamless Communication Across Borders
As we move towards increasingly integrated technological landscapes, the ease of maintaining digital connections while travelling becomes more of a practical reality. The rise of eSIMs and travel SIM cards represents this shift – offering dependability, cost-effectiveness, and the utmost convenience for globetrotters.
In the era of social media, remote work, and digital nomadism, these communication tools are not just about staying online. They’re about sustaining livelihoods, nurturing relationships, and enriching travel experiences through the simple power of connectivity.
Conclusion
The digital age has brought about a revolution in the way we stay connected while exploring new horizons. The simplicity and sophistication of eSIMs, coupled with the tried-and-true reliability of travel SIM cards, have significantly eased the stress of staying online for travellers across Europe and the UK.
As technology continues to advance, we can only anticipate further innovations in the world of international communication. Until then, services like eSIM UK providers and travel SIM card specialists like Travelkon are at the forefront, ensuring that travellers can capture, share, and savour their European adventures with ease and assurance. The horizon for seamless global communication looks promising, and for today’s international traveller, the journey is just as connected as the destination.
Tech
Exploring Humanilex: A Comprehensive Platform for Human Resources Management
In today’s fast-paced business environment, managing human resources efficiently is crucial for any organization. Humanilex, a comprehensive human resources management platform, is designed to streamline HR processes and enhance organizational productivity. This article explores the features, benefits, and unique aspects of Humanilex, demonstrating how it is revolutionizing the HR landscape.
What is Humanilex?
Humanilex is an all-in-one human resources management system (HRMS) that integrates various HR functions into a single platform. It offers a wide range of tools and features to manage employee data, recruitment, payroll, performance management, training, and compliance. By centralizing these functions, Humanilex simplifies HR tasks, reduces administrative burden, and provides valuable insights for strategic decision-making.
Key Features of Humanilex
- Employee Database Management: Humanilex provides a centralized database to store and manage employee information. This includes personal details, job roles, contact information, and employment history. The platform ensures data accuracy and security, making it easy to access and update employee records.
- Recruitment and Onboarding: The recruitment module of Humanilex automates the hiring process, from posting job openings to screening candidates and scheduling interviews. The onboarding feature ensures a smooth transition for new hires, providing them with necessary information and resources to integrate into the company seamlessly.
- Payroll Management: Humanilex simplifies payroll processing by automating calculations, deductions, and tax compliance. It ensures timely and accurate salary disbursements, reducing errors and enhancing employee satisfaction.
- Performance Management: The platform includes tools for setting performance goals, conducting evaluations, and providing feedback. This helps in identifying top performers, addressing areas of improvement, and aligning individual objectives with organizational goals.
- Training and Development: Humanilex offers a comprehensive training management system to facilitate employee development. It enables the creation of training programs, tracking of progress, and assessment of training effectiveness. This ensures that employees acquire the skills needed for their roles and contribute to the company’s growth.
- Compliance and Reporting: Humanilex assists in maintaining compliance with labor laws and industry regulations. It generates reports and analytics, providing insights into HR metrics such as turnover rates, employee satisfaction, and diversity. These reports aid in strategic planning and decision-making.
Benefits of Using Humanilex
- Efficiency and Productivity: By automating routine HR tasks, Humanilex frees up time for HR professionals to focus on strategic initiatives. This boosts overall productivity and operational efficiency.
- Data-Driven Decision Making: Humanilex’s analytics and reporting features provide valuable insights into workforce trends and performance. This data-driven approach enables informed decision-making, helping organizations optimize their HR strategies.
- Enhanced Employee Experience: With streamlined processes and timely support, Humanilex enhances the overall employee experience. From recruitment to retirement, the platform ensures that employees receive the support they need at every stage of their employment.
- Cost Savings: By reducing manual processes and minimizing errors, Humanilex helps in cutting down operational costs. The platform’s efficiency translates into financial savings for the organization.
Unique Aspects of Humanilex
- Customization and Scalability: Humanilex is highly customizable, allowing organizations to tailor the platform to their specific needs. It is also scalable, making it suitable for businesses of all sizes, from startups to large enterprises.
- User-Friendly Interface: The platform boasts an intuitive and user-friendly interface, ensuring ease of use for HR professionals and employees alike. This minimizes the learning curve and encourages widespread adoption within the organization.
- Integration Capabilities: Humanilex integrates seamlessly with other business systems and software, such as ERP and CRM platforms. This ensures a cohesive and unified approach to managing various business functions.
- Support and Training: Humanilex offers robust support and training resources to help users make the most of the platform. This includes customer support, online tutorials, and training sessions to ensure smooth implementation and usage.
Conclusion
Humanilex is transforming the way organizations manage their human resources. With its comprehensive suite of tools and features, it addresses the complexities of HR management while enhancing efficiency and productivity. By leveraging Humanilex, organizations can ensure a streamlined, data-driven approach to HR, ultimately fostering a positive and productive workplace. As the business landscape continues to evolve, platforms like Humanilex will play an integral role in shaping the future of human resources management.
FAQs on Humanilex
1. What is Humanilex?
Humanilex is a comprehensive human resources management system (HRMS) designed to streamline HR processes, including employee database management, recruitment, payroll, performance management, training, and compliance.
2. How does Humanilex help in managing employee data?
Humanilex provides a centralized database to store and manage all employee information, such as personal details, job roles, contact information, and employment history. This ensures data accuracy, security, and easy access for updates and retrieval.
3. Can Humanilex assist with recruitment and onboarding?
Yes, Humanilex automates the recruitment process from posting job openings to screening candidates and scheduling interviews. The onboarding feature ensures new hires have a smooth transition by providing them with the necessary information and resources to integrate into the company.
4. How does Humanilex handle payroll processing?
Humanilex automates payroll processing by calculating salaries, deductions, and ensuring tax compliance. It guarantees timely and accurate salary disbursements, reducing errors and improving employee satisfaction.
5. What tools does Humanilex offer for performance management?
Humanilex includes tools for setting performance goals, conducting evaluations, and providing feedback. These features help identify top performers, address areas for improvement, and align individual objectives with organizational goals.
6. How does Humanilex support employee training and development?
Humanilex offers a training management system that enables the creation of training programs, tracking of progress, and assessment of training effectiveness. This ensures employees acquire the necessary skills for their roles and contribute to the company’s growth.
7. What compliance and reporting features does Humanilex provide?
Humanilex helps maintain compliance with labor laws and industry regulations by generating reports and analytics on HR metrics such as turnover rates, employee satisfaction, and diversity. These reports aid in strategic planning and decision-making.
8. Can Humanilex be customized to fit our organization’s specific needs?
Yes, Humanilex is highly customizable, allowing organizations to tailor the platform to their specific requirements. It is also scalable, making it suitable for businesses of all sizes.
9. Is Humanilex user-friendly?
Yes, Humanilex features an intuitive and user-friendly interface that minimizes the learning curve and encourages widespread adoption among HR professionals and employees.
10. Does Humanilex integrate with other business systems?
Humanilex integrates seamlessly with other business systems and software, such as ERP and CRM platforms, ensuring a cohesive and unified approach to managing various business functions.
11. What kind of support and training does Humanilex offer?
Humanilex provides robust support and training resources, including customer support, online tutorials, and training sessions to help users maximize the platform’s capabilities and ensure smooth implementation and usage.
12. How does Humanilex enhance employee experience?
Humanilex enhances employee experience by streamlining HR processes and providing timely support. From recruitment to retirement, the platform ensures employees receive the necessary support at every stage of their employment.
Tech
Flashata: A Comprehensive Guide to the Innovative Technology

In the ever-evolving landscape of technology, innovations that redefine the way we interact with the digital world are highly sought after. One such groundbreaking innovation is Flashata, a revolutionary technology that is poised to transform various industries. This comprehensive guide delves into what Flashata is, how it works, and its potential applications and benefits.
What is Flashata?
Flashata is an advanced data storage and processing technology that combines the speed of flash memory with the versatility of artificial intelligence (AI). Developed by a team of leading engineers and data scientists, Flashata aims to address the limitations of traditional storage solutions and enhance data processing capabilities.
How Does Flashata Work?
At its core, Flashata utilizes high-speed flash memory to store and retrieve data at unprecedented speeds. What sets Flashata apart is its integration with AI algorithms, which optimize data management and processing in real-time. Here’s a breakdown of its key components:
- Flash Memory: Flashata employs cutting-edge flash memory chips that offer rapid read and write speeds, significantly faster than traditional hard drives and even some solid-state drives (SSDs).
- AI Integration: The integration of AI allows Flashata to intelligently manage data storage. AI algorithms predict data access patterns, optimize storage locations, and streamline data retrieval processes, ensuring maximum efficiency.
- Scalability: Flashata is designed to be highly scalable, making it suitable for various applications, from small-scale personal use to large-scale enterprise solutions.
- Energy Efficiency: Despite its high performance, Flashata is engineered to be energy-efficient, reducing the overall power consumption compared to conventional data storage solutions.
Applications of Flashata
Flashata’s versatility and high performance open up a plethora of applications across different sectors. Here are some of the most promising areas where Flashata can make a significant impact:
- Data Centers: In data centers, speed and efficiency are paramount. Flashata’s ability to handle large volumes of data quickly and efficiently can revolutionize data center operations, reducing latency and improving overall performance.
- Artificial Intelligence: AI applications often require rapid access to vast amounts of data. Flashata’s integration with AI not only accelerates data processing but also enhances the performance of AI models by providing real-time data management.
- Healthcare: The healthcare industry generates massive amounts of data daily. Flashata can facilitate faster data retrieval and processing, aiding in quicker diagnosis, better patient care, and more efficient research and development.
- Finance: Financial transactions and data analysis require high-speed processing to ensure accuracy and efficiency. Flashata’s capabilities can streamline financial operations, from real-time trading to fraud detection.
- Gaming and Entertainment: The gaming industry demands high performance for seamless experiences. Flashata’s speed and efficiency can significantly enhance gaming experiences by reducing load times and improving overall game performance.
Benefits of Flashata
The adoption of Flashata technology brings several benefits, including:
- Unmatched Speed: Flashata’s use of high-speed flash memory ensures rapid data access and processing, reducing latency and improving efficiency.
- Enhanced Performance: The AI integration optimizes data management, resulting in better performance and resource utilization.
- Energy Efficiency: Flashata’s energy-efficient design helps reduce power consumption, contributing to lower operational costs and a smaller environmental footprint.
- Scalability: Flashata’s scalable architecture makes it suitable for a wide range of applications, from personal devices to large-scale enterprise solutions.
- Reliability: Flash memory is known for its durability and reliability. Flashata builds on this foundation, offering a robust and dependable data storage solution.
Conclusion
Flashata represents a significant leap forward in data storage and processing technology. By combining the speed of flash memory with the intelligence of AI, Flashata offers a versatile, scalable, and energy-efficient solution that can transform industries and redefine how we interact with data. As technology continues to advance, innovations like Flashata will undoubtedly play a crucial role in shaping the future of data management and processing.
Flashata FAQs
What is Flashata?
Flashata is an advanced data storage and processing technology that combines high-speed flash memory with artificial intelligence (AI) to optimize data management and processing in real-time.
How does Flashata work?
Flashata utilizes high-speed flash memory for rapid data access and retrieval. It integrates AI algorithms to predict data access patterns, optimize storage locations, and streamline data retrieval processes, ensuring maximum efficiency and performance.
What are the main components of Flashata?
The main components of Flashata include:
- Flash Memory: High-speed flash memory chips for fast data read and write speeds.
- AI Integration: AI algorithms for intelligent data management and processing.
- Scalability: Designed to be scalable for various applications.
- Energy Efficiency: Engineered to reduce power consumption.
What are the benefits of using Flashata?
The benefits of using Flashata include:
- Unmatched Speed: Rapid data access and processing.
- Enhanced Performance: Optimized data management through AI.
- Energy Efficiency: Lower power consumption.
- Scalability: Suitable for a wide range of applications.
- Reliability: Durable and dependable data storage solution.
In which industries can Flashata be used?
Flashata can be used in various industries, including:
- Data Centers: For faster and more efficient data processing.
- Artificial Intelligence: To enhance AI model performance with real-time data management.
- Healthcare: For quicker data retrieval and processing, aiding in better patient care and research.
- Finance: To streamline financial operations, including real-time trading and fraud detection.
- Gaming and Entertainment: To reduce load times and improve game performance.
How does Flashata improve data center operations?
Flashata improves data center operations by providing rapid data access and processing, reducing latency, and optimizing data management through AI, leading to enhanced overall performance and efficiency.
How does Flashata enhance AI applications?
Flashata enhances AI applications by integrating AI algorithms that optimize data storage and retrieval. This accelerates data processing and improves the performance of AI models, providing real-time data management.
Is Flashata energy efficient?
Yes, Flashata is designed to be energy-efficient, reducing overall power consumption compared to traditional data storage solutions, which helps lower operational costs and minimize environmental impact.
Can Flashata be used for personal devices?
Yes, Flashata’s scalable architecture makes it suitable for a wide range of applications, including personal devices, providing high-speed data access and enhanced performance.
What makes Flashata reliable?
Flashata is built on the foundation of flash memory, known for its durability and reliability. The integration of AI further enhances its performance and dependability, making it a robust data storage solution.
How does Flashata compare to traditional storage solutions?
Flashata offers significantly faster data access and processing speeds compared to traditional hard drives and even some solid-state drives (SSDs). Its AI integration optimizes data management, making it more efficient and reliable, while its energy-efficient design reduces power consumption.
Is Flashata suitable for large-scale enterprise solutions?
Yes, Flashata’s scalable design makes it ideal for large-scale enterprise solutions, providing the speed, efficiency, and reliability needed for demanding applications.
How does Flashata handle large volumes of data?
Flashata handles large volumes of data efficiently through its high-speed flash memory and AI algorithms, which optimize data storage and retrieval, ensuring rapid access and processing even for extensive datasets.
What future developments can we expect from Flashata?
Future developments for Flashata may include further advancements in AI algorithms for even greater efficiency, increased storage capacities, and broader applications across more industries as technology continues to evolve.
Where can I learn more about Flashata?
For more information about Flashata, visit the official Flashata website or contact their support team for detailed inquiries and updates on the latest developments and applications.
-

 Health4 months ago
Health4 months agoGorgeous – Definition, Meaning & Synonyms
-

 News4 months ago
News4 months agoIs Ofleaked.net Legit or Scam?
-

 Tech4 months ago
Tech4 months agoGreenbits: Revolutionizing Sustainable Agriculture
-
 Tech4 months ago
Tech4 months agoUnderstanding the 2023-1954
-

 Life Style4 months ago
Life Style4 months agoA Comprehensive Guide to OpenHousePerth.net Insurance
-

 Tech4 months ago
Tech4 months agoGEEKZILLA.TECH HONOR MAGIC 5 PRO REVIEW
-

 Entertainment4 months ago
Entertainment4 months agoOWL EXPRESS LTD. Overview – Companies House
-
![[noblocc] Kicked for Being AFK](https://bicimag.com/wp-content/uploads/2024/03/Noblocc-Kicked-for-Being-AFK-1-400x240.webp)
![[noblocc] Kicked for Being AFK](https://bicimag.com/wp-content/uploads/2024/03/Noblocc-Kicked-for-Being-AFK-1-80x80.webp) News4 months ago
News4 months ago[noblocc] Kicked for Being AFK